Learn Cyber Threat Detection and Security Fundamentals — Cybersecurity Course in Telugu
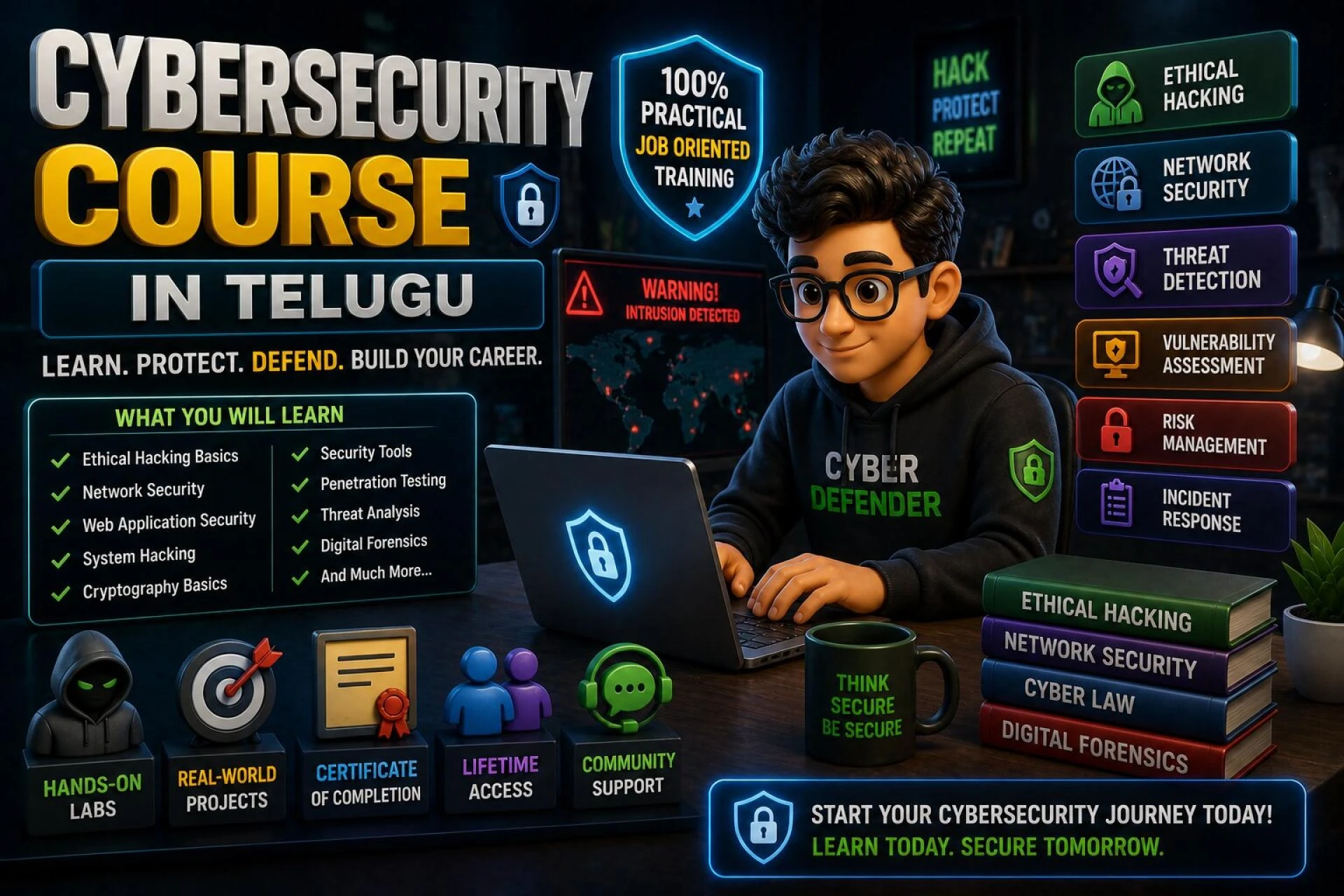
Cybersecurity Course in Telugu

Introduction
Every security breach that makes news headlines began with a threat that went undetected long enough for damage to occur. The average time between an attacker gaining access to a network and that access being discovered is measured in weeks, sometimes months. Organizations that detect threats quickly that catch the early signs of an intrusion before it becomes a breach suffer dramatically less damage than those that discover attacks only after significant harm has occurred. Threat detection is consequently one of the most valued capabilities in cybersecurity, and it starts with fundamentals that every security professional must understand deeply. A Cybersecurity Course in Telugu that covers both cyber threat detection and the foundational security concepts it depends on gives Telugu-speaking freshers a core skill set with immediate career relevance.
Understanding Cyber Threats Before Detecting Them
Detecting a threat requires knowing what you are looking for. That knowledge starts with understanding the threat landscape — the types of attacks, attacker motivations, and attack methodologies that organizations actually face.
Threat Categories Every Security Fresher Must Know
Malware: Malicious software designed to damage systems, steal data, or provide unauthorized access. Categories include viruses, worms, trojans, ransomware, spyware, and rootkits each with distinct behaviors and detection signatures.
Phishing and Social Engineering: Attacks that target human behavior rather than technical vulnerabilities. Phishing emails trick recipients into clicking malicious links or revealing credentials. Spear phishing targets specific individuals with personalized, convincing messages.
Man-in-the-Middle Attacks: An attacker positions themselves between two communicating parties, intercepting and potentially modifying the traffic. These attacks target authentication sessions, financial transactions, and sensitive communications.
Insider Threats: Security risks that originate from within an organization employees, contractors, or partners who misuse their legitimate access. Detecting insider threats requires behavioral analysis rather than traditional perimeter monitoring.
Advanced Persistent Threats (APTs): Sophisticated, long-duration attacks by well-resourced attackers often nation-states or organized criminal groups who maintain persistent access to target networks for months or years.
The Security Fundamentals That Enable Detection
Log Analysis
Every system and network device generates logs records of events that occur during normal and abnormal operation. Threat detection depends on the ability to collect, store, and analyze these logs to find the events that indicate malicious activity.
What log analysis skills involve:
- Understanding what different log types record Windows Security logs, Linux auth logs, firewall logs, DNS logs, web server access logs
- Knowing which events are normal and which are worth investigating failed login attempts, unusual outbound connections, unexpected process execution
- Using tools to search, filter, and correlate logs across multiple sources
- Writing queries that surface specific event patterns associated with known attack techniques
Network Traffic Analysis
Threat detection at the network level means monitoring traffic for patterns that indicate malicious behavior scanning activity, beaconing to command-and-control servers, unusual data volumes moving toward external addresses, lateral movement between internal systems.
Network analysis skills:
- Reading and interpreting packet captures in Wireshark
- Understanding what normal traffic baselines look like for a specific environment
- Identifying the network indicators of common attack types
- Writing network detection rules that catch malicious patterns without overwhelming analysts with false positives
Indicators of Compromise (IOCs)
Security teams share threat intelligence in the form of Indicators of Compromise specific technical artifacts associated with known malicious activity. These include IP addresses of command-and-control servers, file hashes of known malware, domain names used in phishing campaigns, and registry keys associated with specific malware families.
Understanding how to use IOCs importing them into security tools, writing detection rules based on them, and interpreting hits when they occur is a practical skill that SOC roles use daily.
SIEM Operations
Security Information and Event Management platforms are the operational hub of modern threat detection. They collect logs from across an organization's infrastructure, apply detection rules, and present analysts with prioritized alerts for investigation.
A Telugu security course that introduces SIEM concepts even using free platforms like the ELK stack produces freshers who understand the detection pipeline rather than encountering it for the first time on the job.
Why Telugu Makes Threat Detection Concepts Click
Threat detection is as much analytical as it is technical. Understanding why a specific log pattern indicates malicious activity the chain of reasoning from observed event to threat conclusion requires the ability to follow nuanced explanation and ask precise questions when the reasoning is unclear.
These analytical discussions are most productive in a student's native language. A Telugu instructor who walks through a log analysis exercise in Telugu explaining what each event means, why the combination is suspicious, and what an analyst should do next builds the analytical habit more effectively than the same explanation in English for a Telugu-speaking student.
Conclusion
Cyber threat detection and the security fundamentals that enable it are among the most immediately valuable skills a fresher can bring to a security team. A Cybersecurity Course in Telugu that builds genuine threat detection ability through understanding of the threat landscape, log analysis practice, network traffic analysis, IOC usage, and SIEM exposure produces freshers who contribute meaningfully to security operations from their earliest days on the job. Detect threats early. Understand the fundamentals deeply. Build the career on that foundation.
#Cybersecurity Course in Telugu #Ethical Hacking Course in Telugu #Network Security Training
0 comments
Log in to leave a comment.
Be the first to comment.