Understanding the Zero Trust Maturity Model and Why It Matters Now
Understanding the Zero Trust Maturity Model and Why It Matters Now
Security teams no longer ask whether breaches will happen. They ask when and how far attackers will get.
That shift in mindset explains why organizations now rethink trust entirely. Instead of assuming safety inside the network, they verify everything, all the time. This is where the zero trust maturity model becomes essential.
It gives structure to a concept that many teams understand in theory but struggle to apply in practice. This post explains what the model is, how it works, and how organizations can use it to build real, measurable security progress.
Why Zero Trust Needs a Maturity Framework
Zero trust sounds simple: never trust, always verify. In reality, implementation gets messy. Most environments mix legacy systems, cloud platforms, remote users, and third-party tools. Jumping straight into advanced controls without a roadmap leads to gaps and frustration.
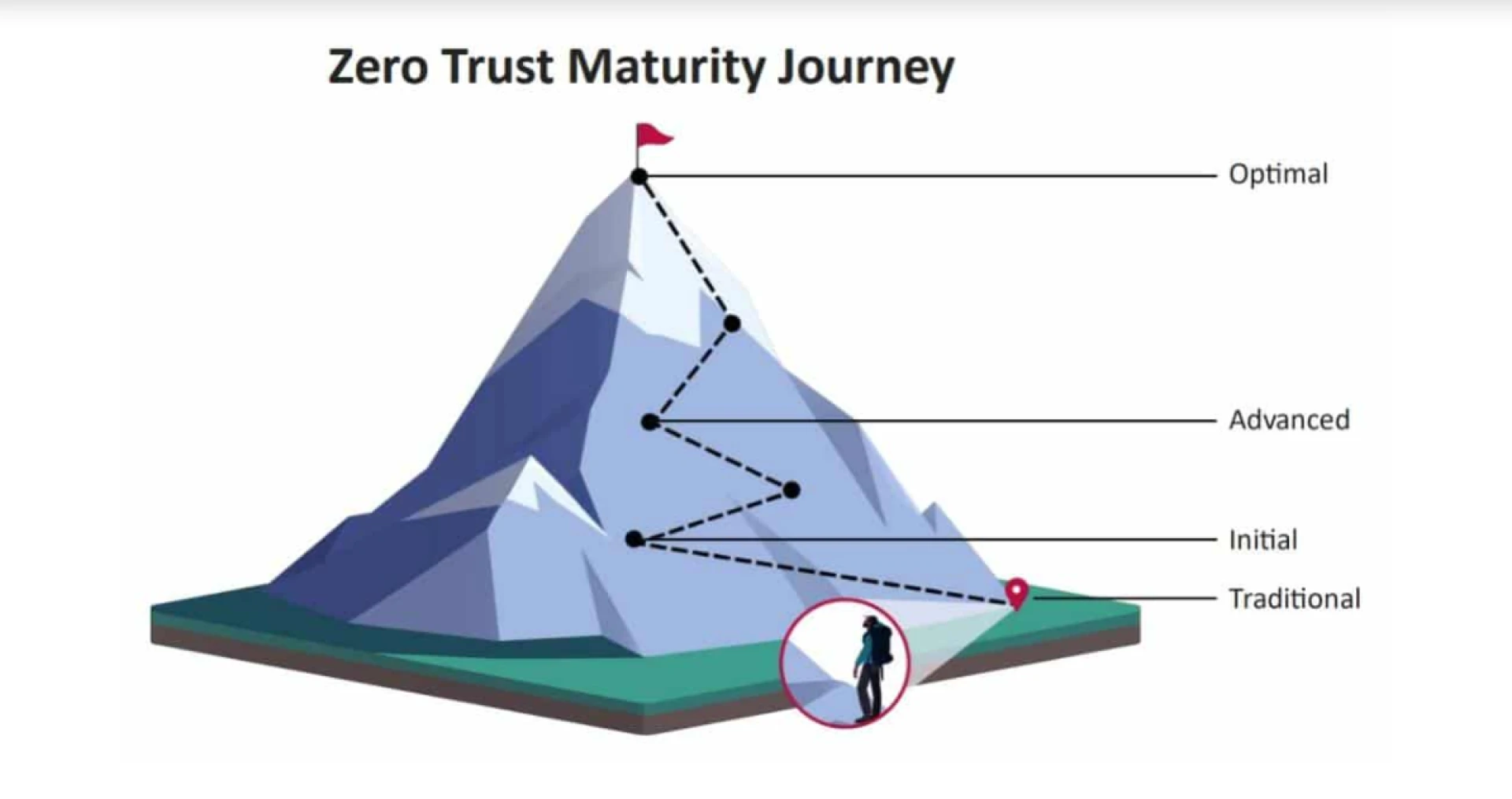
The zero trust maturity model solves this by breaking adoption into stages. Instead of chasing perfection, teams focus on progress. Each stage builds on the last. This approach helps organizations measure where they stand today and decide what to improve next without overwhelming people or budgets.
What the Zero Trust Maturity Model Actually Covers
The model focuses on several core pillars that work together rather than in isolation. These pillars include identity, devices, networks, applications, data, and visibility. Each pillar matures independently, but alignment matters. For example, strong identity controls mean little if network access stays wide open.
The zero trust maturity model encourages balance. It pushes teams to strengthen controls gradually while improving monitoring and response. This layered approach reduces blind spots and limits attacker movement across systems.
Identity as the Starting Point
Identity sits at the center of zero trust. Users, services, and devices must prove who they are before gaining access. Early maturity focuses on basic authentication and access policies. Higher maturity introduces continuous verification and context-based decisions. These decisions consider location, device health, and behavior. As identity matures, attackers lose the ability to move freely, even with stolen credentials.
Device Awareness and Control
Devices tell a story.
- Are they managed?
- Are they patched?
- Are they behaving normally?
The maturity model pushes organizations to move beyond simple device registration. Advanced stages use real-time posture checks and isolate risky devices automatically. This reduces the chance that compromised endpoints become launchpads for deeper attacks.
Network Controls Beyond Traditional Perimeters
Traditional networks trust anything inside the boundary. Zero trust challenges that assumption. Early maturity focuses on basic segmentation. Later stages introduce granular, identity-based network controls.
The zero trust maturity model emphasizes limiting lateral movement. Even if attackers gain access, they cannot roam freely. Each connection requires validation. This dramatically reduces impact during breaches.
Application and Data Protection Alignment
Applications and data often receive uneven protection. Some systems stay locked down, while others remain exposed. The maturity model aligns application access with identity and network controls. It also emphasizes data classification and encryption.
At higher maturity levels, access decisions adapt dynamically. Sensitive data stays protected even when users change roles or locations. This alignment helps organizations meet compliance requirements while improving real security outcomes.
Visibility and Analytics as the Backbone
Zero trust fails without visibility. Teams need to see what’s happening across identities, devices, and networks. Early maturity includes basic logging. Advanced maturity introduces centralized analytics and automated response. The zero trust maturity model highlights visibility as a continuous requirement, not a final step. Better insight leads to faster detection and stronger decision-making.
How Organizations Progress Through Maturity Stages
Most organizations sit between early and intermediate maturity. They may have strong identity controls but weak network segmentation. Or they protect cloud apps well but ignore internal systems.
The model encourages honest assessment. Progress doesn’t require rebuilding everything. It requires prioritization. Teams identify high-risk areas first. They improve controls incrementally. Over time, security becomes proactive rather than reactive.
Common Mistakes During Adoption
Many teams treat zero trust as a product instead of a strategy. Others try to implement everything at once. Both approaches fail. The maturity model exists to prevent this. It promotes realistic timelines and achievable goals. Another common mistake involves ignoring user experience. Controls must protect without blocking productivity. Successful programs balance security with usability.
Why Government Guidance Influences Private Sector Strategy
Government frameworks often shape broader security practices. The zero trust maturity model reflects lessons learned from large, complex environments. These environments face constant threats and strict compliance requirements. When private organizations adopt similar frameworks, they benefit from proven approaches. This alignment also helps organizations working with regulated industries or public sector partners.
FAQ
Is Zero Trust Only for Large Organizations?
No. Organizations of any size can adopt it. The maturity model helps smaller teams prioritize controls based on risk.
How Long Does It Take to Mature Zero Trust?
It varies. Most organizations progress over years, not months. The goal is steady improvement, not speed.
Does Zero Trust Replace Existing Security Tools?
Not always. It often integrates with existing tools and improves how they work together.
Can Zero Trust Stop All Breaches?
No security model can stop everything. Zero trust focuses on reducing impact and limiting spread.
Where Should Organizations Start?
Start with identity and visibility. These areas provide the foundation for everything else.
Conclusion
Security maturity doesn’t happen overnight. It happens through deliberate, informed decisions. The zero trust maturity model gives organizations a practical way to move forward without guesswork. Instead of chasing trends, teams build layered defenses that adapt to change.
By strengthening identity, controlling access, limiting movement, and improving visibility, organizations create environments where attackers struggle to succeed. Zero trust works best when treated as a journey, not a destination. The sooner that journey starts, the stronger the long-term security posture becomes.
0 comments
Log in to leave a comment.
Be the first to comment.