How to Build a Fair and Secure RNG for Your Multiplayer Poker Game?
How to Build a Fair and Secure RNG for Multiplayer Poker Games

Building a multiplayer poker game that players trust isn't just about slick graphics and smooth gameplay; it's fundamentally about fairness. At the heart of any reputable online poker platform lies a robust Random Number Generator (RNG) that ensures every card dealt, every shuffle, and every outcome is genuinely unpredictable and fair. Without this critical component, even the most feature-rich poker game will fail to retain players who quickly lose trust when they suspect the deck might be stacked against them.
The challenge of implementing a truly secure and fair RNG system goes beyond simple randomisation. It requires understanding cryptographic principles, implementing proper seeding mechanisms, ensuring server-client integrity, and creating transparent verification systems that players can trust. Whether you're an independent developer creating your first poker app or a gaming studio scaling up to handle thousands of concurrent players, the decisions you make about your RNG implementation will directly impact your game's reputation and success.
This comprehensive guide will walk you through every aspect of building a fair and secure RNG for your multiplayer poker game. You'll learn the fundamental concepts behind randomness in gaming, explore different RNG algorithms and their trade-offs, understand critical security considerations, and discover implementation strategies that balance performance with cryptographic strength. We'll also cover testing methodologies, regulatory compliance requirements, and best practices that leading poker platforms use to maintain player trust.
Understanding RNG in Online Poker Games
True randomness in digital systems is a paradox; computers are deterministic machines that follow precise instructions, making genuine randomness impossible without external input. In poker games, fairness doesn't require true randomness but rather unpredictability that's mathematically indistinguishable from random chance.
A fair RNG produces outcomes where:
- Each possible card has an equal probability of being dealt
- Previous outcomes don't influence future results
- No player or system can predict upcoming cards
- The distribution of outcomes matches mathematical expectations over time
The concept of fairness extends beyond mathematical randomness. Players need confidence that the system isn't manipulated to favor the house, certain players, or create artificial "action" hands. This psychological aspect of fairness is why transparency and verifiability become crucial components of any RNG system.
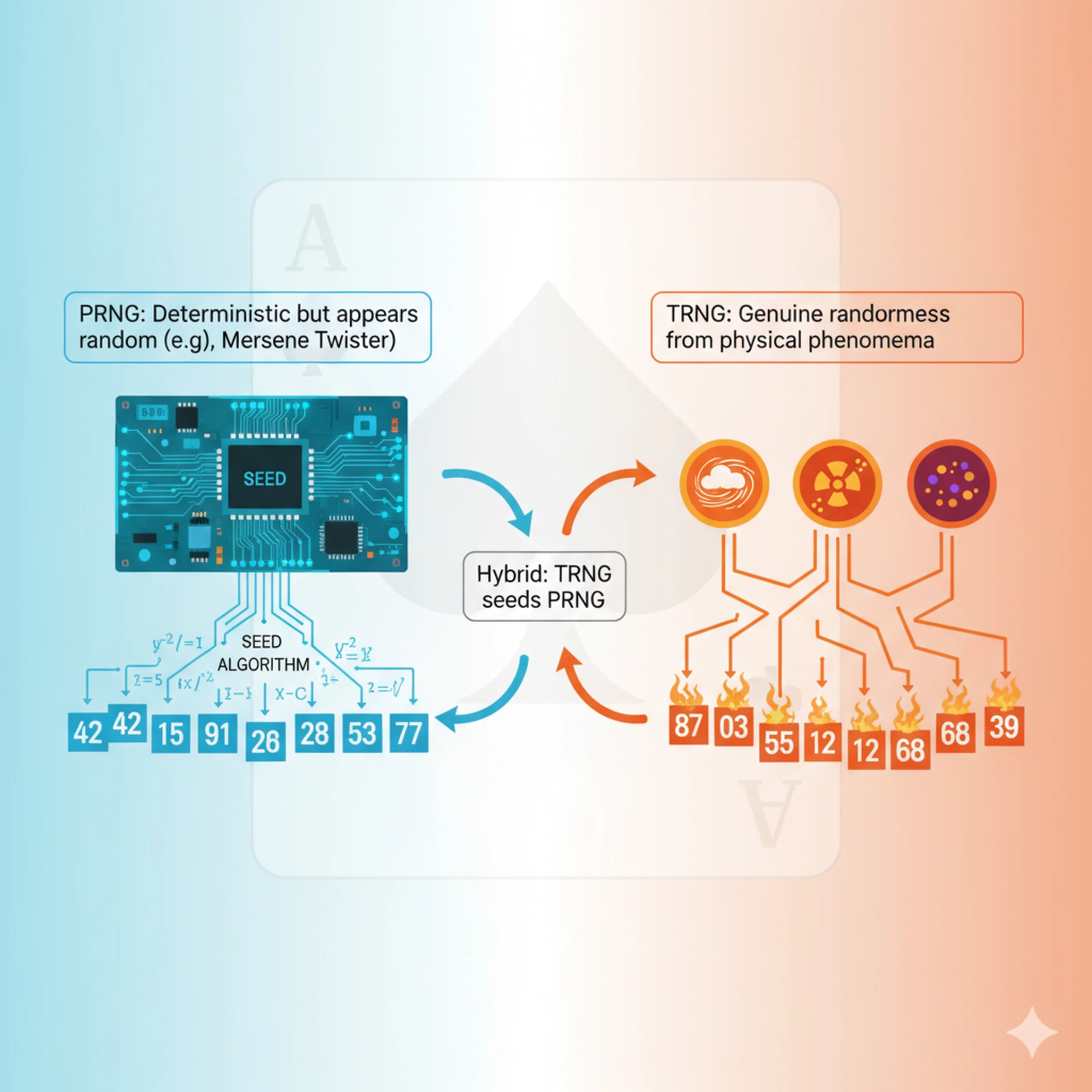
The Difference Between PRNG and TRNG
Pseudo-Random Number Generators (PRNGs) form the backbone of most online poker platforms. These algorithms use mathematical formulas to generate sequences of numbers that appear random but are actually deterministic. Given the same initial seed value, a PRNG will always produce the same sequence. Modern PRNGs like Mersenne Twister or PCG (Permuted Congruential Generator) can produce sequences with periods so long that they're effectively random for gaming purposes.
True Random Number Generators (TRNGs) derive randomness from physical phenomena like atmospheric noise, radioactive decay, or quantum effects. While TRNGs provide genuine unpredictability, they're typically slower and more complex to implement than PRNGs. Many poker platforms use a hybrid approach, using TRNG-generated seeds to initialize their PRNG algorithms, combining the unpredictability of hardware randomness with the speed and reliability of software generation.
Why Standard Random Functions Aren't Sufficient?
Using standard library random functions like Math.random() in JavaScript or rand() in C++ might seem convenient, but they're catastrophically inadequate for poker games. These functions typically use simple linear congruential generators with short periods, predictable patterns, and poor statistical properties. More critically, they're often initialized with easily guessable seeds like system time, making them vulnerable to prediction attacks.
Standard random functions also lack cryptographic security, meaning an attacker who observes enough outputs can potentially determine the internal state and predict future numbers. In a poker context, this could allow cheating through card prediction, devastating both game integrity and player trust.
Core Components of a Secure RNG System
Cryptographically Secure Random Number Generation
Cryptographically Secure Pseudo-Random Number Generators (CSPRNGs) represent the gold standard for poker game randomness. Unlike standard PRNGs, CSPRNGs are designed to withstand sophisticated attacks where adversaries have partial knowledge of the generator's output. Modern poker platforms employ sophisticated algorithms to generate truly random numbers, ensuring that every player receives cards selected from a thoroughly shuffled deck. Random Number Generation Evolving Poker: RNG.
Key characteristics of CSPRNGs include:
- Unpredictability: Even with knowledge of previous outputs, predicting future values remains computationally infeasible
- Uniform distribution: All possible outputs have equal probability
- Large internal state: Sufficient entropy to prevent state reconstruction attacks
- Forward secrecy: Compromising the current state doesn't reveal previous outputs
Popular CSPRNG implementations for poker games include ChaCha20, Fortuna, and ISAAC. Many platforms also use SHA1 (Secure Hash Algorithm) generators, which are cryptographically secure, randomizing the initial vector, or creating a highly non-deterministic funct. Ion Silver Sands Poker - Security.
Proper Seeding Mechanisms
The strength of any PRNG depends critically on its initial seed. Even the most sophisticated algorithm becomes predictable if initialized with a weak seed. Professional poker platforms implement multi-source seeding strategies that combine:
Hardware entropy sources: Reading from /dev/urandom on Linux systems or CryptGenRandom on Windows provides operating system-level randomness collected from hardware interrupts, disk timings, and other unpredictable system events.
Environmental entropy: Network packet timings, user input patterns, and system load variations add additional unpredictability. However, these sources should supplement, not replace, proper cryptographic entropy.
Time-based components: While system time alone is insufficient, high-resolution timestamps (nanosecond precision) combined with other entropy sources add useful variability.
Player-contributed randomness: Some platforms allow players to contribute to the seed generation process, either through mouse movements during shuffling or by submitting random values that get mixed into the seed pool.
Server-Side vs Client-Side Generation
The architecture decision between server-side and client-side RNG generation fundamentally impacts both security and scalability. Server-side generation, the industry standard, maintains complete control over the randomness process. All RNG operations occur on secure servers, with only the results transmitted to clients. This approach prevents client-side manipulation but requires robust server infrastructure to handle the computational load.
Client-side generation might seem appealing for reducing server load, but it's fundamentally insecure for multiplayer poker. Malicious clients could manipulate their RNG to gain unfair advantages, and synchronizing randomness across multiple clients introduces complex vulnerabilities.
A hybrid approach uses client-contributed entropy for seeding while maintaining server-side generation. This provides transparency and player involvement without compromising security. Some blockchain-based poker platforms extend this concept using decentralized RNG protocols where multiple parties contribute to randomness generation.
Implementation Strategies
Algorithm Selection and Configuration
Choosing the right RNG algorithm requires balancing cryptographic security, performance, and implementation complexity. Popular choices include stream ciphers like Salsa20 or ChaCha (often with the number of rounds reduced to 8 for speed), ISAAC, HC-128, and block ciphers in counter mode such as AES. List of random number generators - Wikipedia.
Mersenne Twister (MT19937), despite its popularity, isn't suitable for poker games as a standalone solution. While it has an enormous period (2^19937-1) and excellent statistical properties, it lacks cryptographic security. Observing 624 consecutive outputs allows complete state reconstruction, making it vulnerable to prediction attacks.
PCG (Permuted Congruential Generator) offers better performance and security than Mersenne Twister. The PCG family is a more modern long-period generator, with better cache locality, and less detectable bias using modern analysis methods, as Mersenne Twister - Wikipedia. PCG combines a linear congruential generator with output permutation, providing good statistical properties and reasonable resistance to prediction.
ChaCha20 represents the cryptographic gold standard for poker RNG. As a stream cipher, it provides both excellent randomness and cryptographic security. ChaCha20/8 offers exceptional performance,e while ChaCha20/20 is a more conservative choice for applications requiring maximum security. PCG – A Family of Better Random Number Generators | Hacker News. The algorithm's seekability allows efficient parallel generation and state management.
For production poker platforms, implementing a layered approach works best:
- Use ChaCha20 or AES-CTR as the primary CSPRNG
- Periodically reseed with fresh entropy from the operating system
- Implement a backup PRNG (like PCG) for non-critical operations
- Monitor and log all RNG operations for audit purposes
Shuffling Algorithms for Card Games
The Fisher-Yates shuffle (also known as the Knuth shuffle) remains the gold standard for card shuffling in poker games. This algorithm guarantees that every possible permutation of the deck has equal probability, provided the underlying RNG is unbiased. The modern inside-out version operates in O(n) time with O(1) extra space:
Here's the javascript:
function fisherYatesShuffle(deck) {
for (let i = deck.length - 1; i > 0; i--) {
const j = secureRandom(0, i + 1);
[deck[i], deck[j]] = [deck[j], deck[i]];
}
return deck;
}
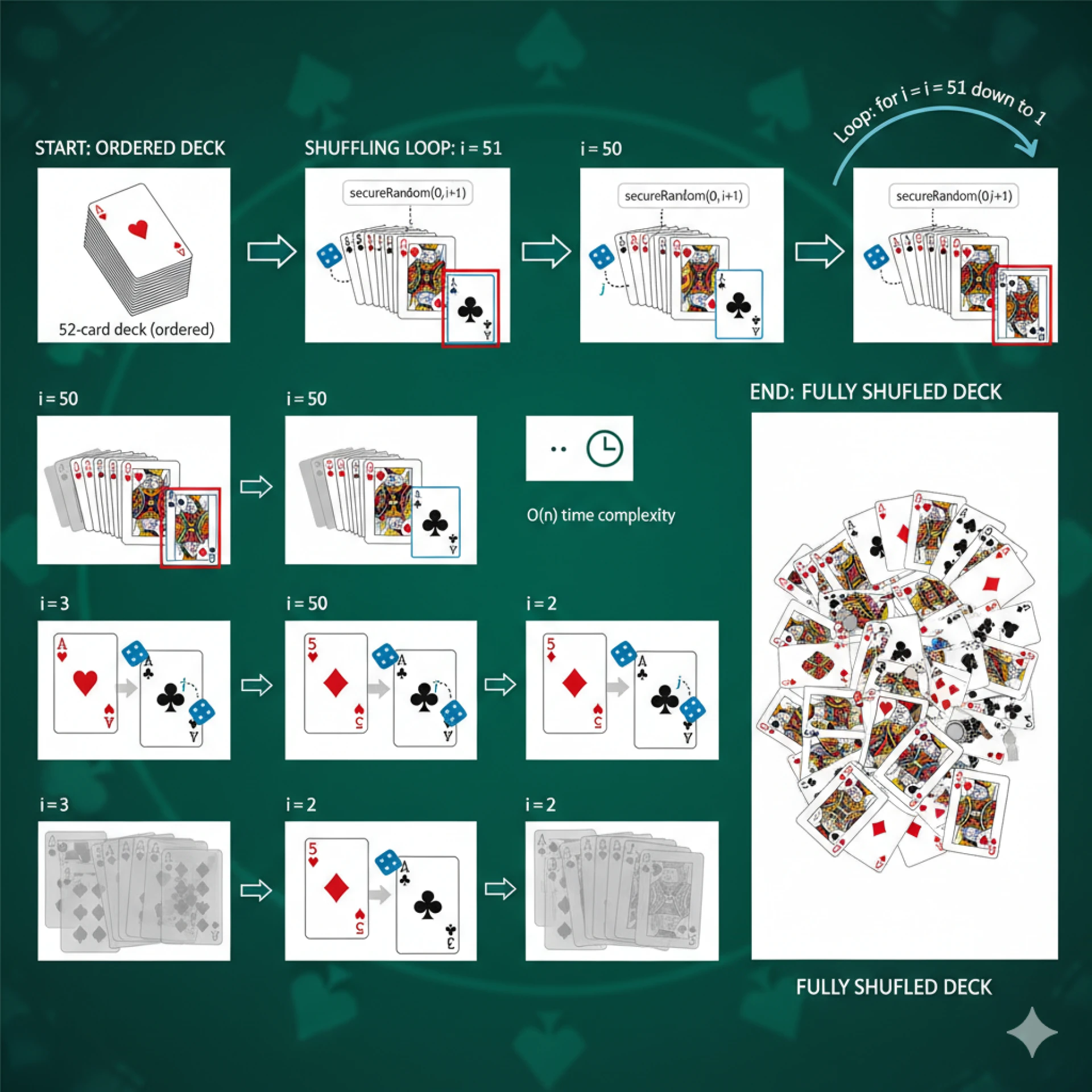
Critical implementation considerations include:
- Avoiding modulo bias: When generating random indices, ensure the random range maps uniformly to the required range
- Complete shuffling: Some platforms perform multiple shuffle passes for psychological reassurance, though one proper shuffle is mathematically sufficient
- Shuffle verification: Log shuffle operations with timestamps and seeds for later verification
- Pre-shuffling: Generate and store shuffled decks in advance during low-load periods to reduce latency during gameplay
Dealing With Entropy Depletion
Entropy depletion occurs when your RNG exhausts its pool of unpredictable data, potentially compromising randomness quality. This risk increases during high-traffic periods when thousands of games simultaneously request random numbers. Implementing robust entropy management prevents this critical failure:
Entropy monitoring systems track available entropy levels in real-time. On Linux systems, monitoring /proc/sys/kernel/random/entropy_avail provides insights into system entropy health. When levels drop below safe thresholds, the system should throttle non-critical random operations or switch to backup entropy sources.
Entropy pooling maintains multiple independent entropy sources that feed into a central mixing pool. The Fortuna algorithm exemplifies this approach, using 32 separate entropy pools that contribute to seed generation at different rates, ensuring long-term unpredictability even if some sources become compromised.
Entropy stretching techniques like key derivation functions (KDFs) can safely expand limited entropy into larger amounts of pseudorandom data. However, this must be done carefully; stretching doesn't add entropy, only distributes it more uniformly.
Security Considerations and Attack Vectors
Common RNG Vulnerabilities in Poker Games
Historical poker platform breaches reveal common vulnerability patterns that developers must avoid. Early platforms like Planet Poker published source code that security experts quickly found flaws in the RNG in Poker: How Does the Random Number Generator Work? - His Hands, demonstrating the importance of proper security auditing.
Insufficient entropy at startup represents a critical vulnerability window. Systems that initialize RNG immediately after boot may lack sufficient entropy, producing predictable initial outputs. Implementing entropy health checks and delaying game availability until adequate entropy accumulates prevents this attack vector.
State exposure through side channels allows attackers to infer RNG state through timing attacks, power analysis, or electromagnetic emissions. While primarily concerning hardware implementations, software systems must also consider timing-based side channels, especially in shared hosting environments.
Weak seed generation remains surprisingly common. Using predictable seeds like timestamps, process IDs, or sequential values allows attackers to drastically reduce the search space for predicting future outputs. Even combining multiple weak sources doesn't necessarily produce strong seeds if the sources are correlated or predictable.
Preventing Prediction and Manipulation Attacks
Building robust defenses against RNG attacks requires multiple security layers:
State isolation ensures the RNG state remains inaccessible to external processes. Use operating system security features like memory protection, process isolation, and secure enclaves when available. Never expose internal state through logs, error messages, or debugging interfaces.
Regular reseeding limits the window of vulnerability if the state becomes compromised. Implement automatic reseeding at regular intervals (every few minutes) and after significant events (new player connections, tournament starts). Each reseed should incorporate fresh entropy from multiple sources.
Output filtering prevents information leakage through RNG outputs. Never directly expose raw RNG output to clients; always transform it through one-way functions or use it as input to higher-level operations like shuffling.
Rate limiting prevents attackers from collecting enough outputs to reconstruct the state. Implement per-player and per-session limits on random number requests, and monitor for suspicious patterns that might indicate state reconstruction attempts.

Audit Trails and Verification Systems
Comprehensive audit systems build player trust and enable investigation of disputed hands. Modern platforms focus on ensuring the integrity of the RNG by isolating it from re-entry, ensuring that once the 52-card deck is randomized and the initial cards are dealt, can this Problem be solved? In | Poker Community, Online Poker Forums, the sequence remains immutable and verifiable.
Cryptographic commitments allow platforms to prove fairness without revealing future cards. Before each hand, the server generates a commitment (hash) of the shuffled deck and shares it with players. After the hand completes, revealing the deck and seed allows players to verify the commitment and confirm no manipulation occurred.
Immutable logging creates tamper-proof records of all RNG operations. Use append-only databases or blockchain-based logging to store:
- Seed values and generation timestamps
- Shuffle operations and resulting deck orders
- Player actions and game outcomes
- System events affecting RNG state
Third-party verification provides independent validation of RNG fairness. Regular audits by certified testing laboratories verify both the implementation correctness and statistical properties of generated sequences. Publishing audit reports and certifications builds player confidence.
Testing and Validation
Statistical Testing Suites
Rigorous statistical testing ensures your RNG produces genuinely random outputs across all operating conditions. Industry-standard test suites evaluate different aspects of randomness:
NIST Statistical Test Suite provides 15 tests examining various statistical properties, including frequency, runs, spectral analysis, and linear complexity. Each test produces a p-value indicating whether the sequence appears random. Multiple sequences should be tested, with at least 99% passing each test for cryptographic applications.
TestU01 offers more comprehensive testing with its SmallCrush, Crush, and BigCrush batteries. BigCrush's 106 stringent tests can detect subtle biases that other suites might miss. However, passing TestU01 doesn't guarantee cryptographic security; it only confirms statistical quality.
PractRand excels at detecting patterns in very large sequences (terabytes of data). Testing shows that some popular generators like xoroshiro128+ and xorshift128+ fail PractRand tests quickly due to non-randomness in the least significant bits. Testing RNGs with PractRand: Xoroshiro, Xorshift, MT, PCG, highlighting the importance of comprehensive testing.
Dieharder extends the original Diehard tests with additional statistical measures. Its ability to test different bit depths and data interpretations helps identify generator weaknesses under various usage patterns.
Distribution Analysis and Chi-Square Tests
Beyond standard test suites, poker-specific distribution analysis ensures fair gameplay:
Card distribution testing verifies that each card appears with equal frequency across millions of deals. Chi-square tests compare observed frequencies against the expected uniform distribution, flagging any statistical anomalies.
Hand frequency analysis confirms poker hands occur at mathematically expected rates. Royal flushes should appear approximately once per 649,740 hands, while pairs should occur in about 42% of five-card deals. Significant deviations indicate RNG problems or implementation errors.
Position fairness testing ensures dealing position doesn't affect card quality. Statistical analysis across millions of hands should show no correlation between seat position and hand strength, confirming positional fairness.
Performance Benchmarking
RNG performance directly impacts game scalability and player experience. Comprehensive benchmarking identifies bottlenecks and optimization opportunities:
A) Throughput testing measures random number generation speed under various loads. Modern CSPRNGs should generate millions of random numbers per second on standard hardware. ChaChaRng provides excellent performance with a relatively small 136 bytes of state. Our RNGs - The Rust Rand Book, making it ideal for high-throughput applications.
B) Latency profiling examines response times for individual operations. Card dealing should complete in microseconds, with shuffling taking no more than milliseconds, even for multiple decks. Profile both the average and worst-case scenarios.
C) Concurrency testing evaluates RNG behavior under parallel access. Thread-safe implementations must maintain randomness quality and performance when multiple games request random numbers simultaneously. Test with realistic player loads and traffic patterns.
D) Resource consumption monitoring tracks CPU, memory, and entropy usage. Efficient RNG implementations minimize resource overhead while maintaining security. Monitor for memory leaks, excessive CPU spikes, or entropy starvation during extended operation.
Best Practices and Industry Standards
Regulatory Compliance Requirements
Operating legal online poker requires meeting strict regulatory standards that vary by jurisdiction. Understanding and implementing these requirements ensures smooth licensing and operation:
GLI-19 (Gaming Laboratories International) Standards represent the most widely accepted testing criteria for online gaming RNGs. These standards mandate specific statistical tests, security requirements, and implementation guidelines. Compliance demonstrates commitment to fair play and facilitates multi-jurisdictional licensing.
eCOGRA (eCommerce Online Gaming Regulation and Assurance) certification provides independent verification of RNG fairness and security. Regular audits, including source code review and live system testing, maintain ongoing compliance. Publishing eCOGRA seals builds player trust and satisfies many regulatory requirements.
ISO/IEC 27001 certification demonstrates comprehensive information security management, including RNG systems. While not poker-specific, this standard shows commitment to security best practices and helps meet data protection regulations.
Regional requirements add complexity. European markets often require local certification, while US states mandate specific testing laboratories. Partnering with experienced poker game development services can navigate these complex regulatory landscapes and ensure compliant implementation from the start.
Transparency and Player Trust
Building lasting player trust requires transparency beyond mere regulatory compliance:
Public RNG documentation explaining your randomness generation process in accessible terms helps players understand fairness measures. Avoid revealing implementation details that could compromise security, but provide enough information to demonstrate commitment to fair play.
Real-time verification tools allow players to verify hand fairness immediately after play. Providing deck seeds, shuffle algorithms, and verification scripts empowers players to independently confirm that no manipulation occurred.
Statistical dashboards displaying long-term RNG performance metrics demonstrate ongoing fairness. Show distributions of hands, cards, and outcomes across millions of games, allowing players to see mathematical fairness in action.
Open-source components, where security permits, can build trust through transparency. While core RNG implementation might remain proprietary, publishing shuffling algorithms, verification tools, or statistical analysis code shows confidence in your system's fairness.
Continuous Monitoring and Updates
RNG security requires ongoing vigilance beyond initial implementation:
Automated monitoring systems continuously analyze RNG output for statistical anomalies. Machine learning algorithms can detect subtle patterns that might indicate degradation or compromise. Alert systems should trigger immediate investigation of any deviations from expected behavior.
Regular security updates patch vulnerabilities and incorporate cryptographic advances. Subscribe to security advisories for all RNG components and maintain update procedures that minimize downtime while ensuring security.
Periodic re-certification maintains regulatory compliance and identifies potential issues before they affect players. Annual audits by independent testing laboratories should examine both technical implementation and operational procedures.
Player feedback integration provides real-world testing beyond automated systems. Establish clear channels for reporting suspected RNG issues and investigate all credible concerns promptly. Even false alarms provide opportunities to improve transparency and build trust.
Advanced Techniques and Future Considerations
Blockchain and Decentralized RNG
Blockchain technology offers secure, decentralized RNG and crypto integration for modern poker platforms. CoinPoker: A Blockchain-Powered Revolution in Online Poker - Eye On Annapolis, representing a paradigm shift in how randomness is generated and verified. Decentralized RNG eliminates single points of failure and provides unprecedented transparency.
Commit-reveal schemes on blockchain enable provably fair randomness without trusted third parties. Players submit encrypted random values that combine to generate unpredictable seeds. Smart contracts ensure no party can manipulate outcomes after commitment.
Verifiable Random Functions (VRFs) provide cryptographic proofs that random numbers were generated correctly. Each random output includes a proof that anyone can verify, ensuring the house cannot manipulate results while maintaining unpredictability.
Decentralized entropy pools aggregate randomness from multiple independent sources, players, validators, and external oracles. This approach ensures no single entity controls randomness generation, addressing trust concerns in traditional centralized systems.
Quantum Random Number Generators
Quantum mechanics offers truly random number generation through fundamental physical processes. While currently expensive and complex, quantum RNG (QRNG) represents the future gold standard for high-security applications:
Quantum entropy sources harvest randomness from quantum phenomena like photon arrival times, radioactive decay, or vacuum fluctuations. These processes are fundamentally unpredictable, providing perfect randomness limited only by measurement precision.
Hybrid quantum-classical systems combine QRNG seeds with classical CSPRNGs for practical implementation. This approach provides quantum-grade entropy while maintaining the performance necessary for real-time gaming.
Cloud-based QRNG services make quantum randomness accessible without specialized hardware. APIs from quantum computing providers offer certified quantum random numbers, though latency and availability remain challenges for real-time gaming applications.
Conclusion
Building a fair and secure RNG system for multiplayer poker represents one of the most critical challenges in online gaming development. The integrity of your random number generation directly determines whether players trust your platform with their time and money. Throughout this guide, we've explored the fundamental principles, implementation strategies, and security considerations that separate amateur attempts from professional-grade poker platforms.
The journey from understanding basic PRNG concepts to implementing production-ready systems reveals the complexity hidden behind seemingly simple card shuffles. Successful implementation requires carefully balancing multiple factors: cryptographic security that prevents prediction attacks, performance that enables smooth gameplay for thousands of concurrent users, regulatory compliance that satisfies licensing requirements, and transparency that builds lasting player trust.
Key takeaways for implementing your poker RNG system include the critical importance of using cryptographically secure algorithms like ChaCha20 rather than standard random functions, implementing proper entropy management with multiple sources and regular reseeding, maintaining comprehensive audit trails that enable verification without compromising security, and conducting rigorous testing using multiple statistical suites and poker-specific distribution analysis. Remember that RNG security isn't a one-time implementation but an ongoing process requiring continuous monitoring, regular updates, and periodic re-certification.
As the online poker industry evolves, new technologies like blockchain-based verification and quantum random number generation promise even greater fairness and transparency. However, the fundamental principles remain constant: players must trust that every card dealt is truly random and that the game is completely fair.
Whether you're building a small poker app or scaling to support millions of players, investing in robust RNG implementation pays dividends in player trust and platform reputation. The technical challenges are significant, but the reward, a thriving poker platform that players trust and enjoy, makes the effort worthwhile. With careful attention to the principles and practices outlined in this guide, you can build an RNG system that not only meets today's standards but remains secure and trusted as your platform grows.
0 comments
Log in to leave a comment.
Be the first to comment.